20 Pro Suggestions For Picking A Zk-Snarks Privacy Website
Wiki Article
The ZK-Powered Shield: What Zk-Snarks Can Hide Your Ip Address And Your Identity From The World
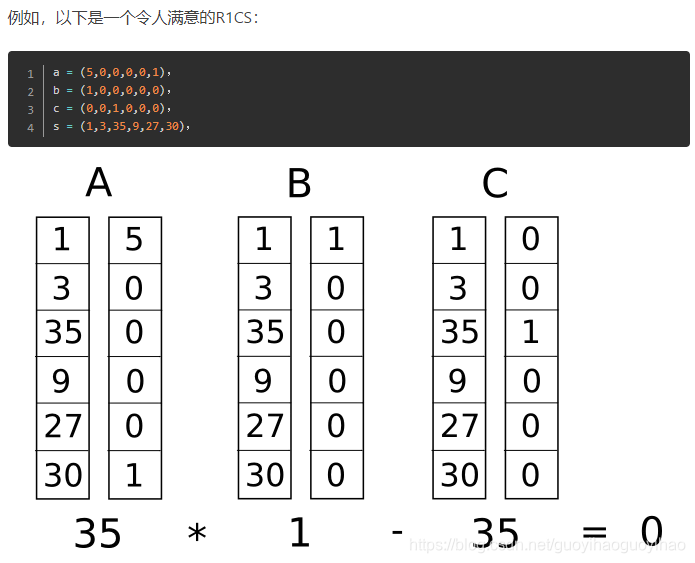
For many years, privacy instruments employ a strategy of "hiding in the crowd." VPNs direct users to another server. Tor sends you back and forth between several nodes. They're effective, however they hide their source through moving it and not by showing it does not need to be made public. zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge) introduce a radically different method of reasoning: you could prove you're authorized for an action to be carried out while not divulging what authorized party that you're. With Z-Text, that you are able broadcast a message for the BitcoinZ blockchain, and the system can prove that you're a genuine participant, with valid shielded addresses, but cannot identify the address you used to send it. Your IP address, identity, your existence in the exchange becomes unknowable mathematically to the observer, yet it is proven to be legitimate for the protocol.
1. The Dissolution of the Sender-Recipient Link
Even with encryption, reveals the connection. Uninitiated observers can tell "Alice is chatting with Bob." Zk-SNARKs make this connection impossible. When Z-Text announces a shielded transaction in zk-proof, it proves an operation is genuine, that is to say you have enough funds and keys that are correct, but does not divulge addresses of the sender and the recipient's address. For an outsider, it is seen as a security-related noise that comes in the context of the network itself and it is not originating from any individual participant. The connection between two particular individuals becomes difficult to determine.
2. IP Protecting IP addresses at the Protocol Level, and not the App Level
VPNs as well as Tor secure your IP via routing the traffic through intermediaries. However, these intermediaries then become points of trust. Z-Text's implementation of zk_SNARKs is a guarantee that your IP is never material in the verification process. When you transmit your protected message to the BitcoinZ peer to peer network, then you are one of thousands of nodes. It is zk-proof, which means that observers observe the transmissions on the network, they cannot be able to connect the received message to the specific wallet that is the originator, as the document doesn't have that info. The IP's information is irrelevant.
3. The Abrogation of the "Viewing Key" Conundrum
In most blockchain privacy systems there is the option of having a "viewing key" that lets you decrypt transaction details. Zk-SNARKs, which are part of Zcash's Sapling protocol which is employed by Ztext can be used to allow selective disclosure. The ability to show someone they sent you a message but without sharing your IP, all of your transactions or even the full content of the message. This proof is the only information being shared. This kind of control is impossible for IP-based systems because revealing the message inherently reveals the location of the source.
4. Mathematical Anonymity Sets That Scale Globally
In a mixing solution or a VPN that you use, your privacy is limited to the other users within that pool at that time. The zk-SNARKs program guarantees your anonymity. will be guaranteed by every shielded address within the BitcoinZ blockchain. Because the verification proves the sender is *some* shielded address among potentially millions of addresses, yet gives no clue as to which one, your privacy scales with the entire network. There is no privacy in one small group of fellow users however, you are part of a massive crowd of cryptographic identities.
5. Resistance against Traffic Analysis and Timing Attacks
Sophisticated adversaries don't just read IP addresses. They also study pattern of activity. They analyze who is sending data, when and how they correlate to the exact timing. Z-Text's use and implementation of zkSARKs as well as a blockchain mempool that allows for the separation of operations from broadcast. You can construct a proof offline and publish it afterward or even a central node send the proof. Its timestamp for being included in a block is not always correlated to the time you created it, leading to a break in timing analysis that usually blocks simpler anonymity methods.
6. Quantum Resistance Through Hidden Keys
They are not quantum resistant. However, should an adversary capture your information now and then break your encryption later and link them to you. Zk-SNARKs, which are used in Z-Text, shield your keys. Your public key is never divulged on the blockchain since the proof assures you're holding the correct keys without showing it. Quantum computers, some time in the future, could have only proof of your identity, however, not the keys. Your past communications remain private because the secret key used secure them wasn't exposed for cracking.
7. Unlinkable Identities across Multiple Conversations
With a single wallet seed will allow you to make multiple secured addresses. Zk's SNARKs lets you show to be the owner or more addresses, but without telling which. So, you may have several conversations in ten other people. However, no individual, or even the blockchain itself can trace those conversations to the exact wallet seed. The social graph of your network can be mathematically separated by design.
8. End of Metadata as a security feature
Inspectors and spies frequently state "we don't require the content and metadata." Ip addresses serve as metadata. The people you speak to are metadata. Zk-SNARKs is unique among privacy solutions because they disguise metadata at the cryptographic level. It is not possible to find "from" and "to" fields, which are in plain text. It is not a metadata-based serve a subpoena. It is only the factual evidence. This will only show that an incident occurred, not the parties.
9. Trustless Broadcasting Through the P2P Network
In the event that you choose to use VPNs VPN You trust that the VPN provider to not record your. While using Tor you are able to trust the exit node's ability to not spy. With Z-Text, you broadcast your zk-proof transaction to the BitcoinZ peer-to-peer network. You connect to a few random nodes, broadcast the details, then break off. The nodes don't learn anything because their proofs reveal nothing. There is no way to be certain that you're the person who started it all, due to the fact that you could be relaying for someone else. A network will become an insecure provider of personal information.
10. The Philosophical Leap: Privacy Without Obfuscation
Finally, zk-SNARKs represent one of the most philosophical transitions away from "hiding" for "proving with no disclosure." Obfuscation techniques recognize that the truth (your Identity, your IP) can be dangerous and needs to be kept secret. Zk-SNARKs accept that the truth isn't important. A protocol must only acknowledge that you're legitimately authorized. This transition from hiding your identity and proactive relevance forms central to the ZK-powered protection. Your IP and identification do not remain hidden. They only serve to enhance the functioning of your network hence they're not ever requested in any way, nor are they transmitted, or exposed. See the most popular zk-snarks for blog recommendations including encrypted text message app, private text message, encrypted message, purpose of texting, messages in messenger, encrypted message in messenger, purpose of texting, text messenger, private text message, phone text and more.
Quantum-Proofing Your Chats: Why Z-Addresses And Zk-Proofs Resist Future Encryption
Quantum computing often is discussed in abstract terms, as a boogeyman which will destroy encryption completely. But the reality is specific and crucial. Shor's method, when ran by a powerful quantum computer, might theoretically break the cryptography based on elliptic curves that protects the majority of internet and blockchain today. However, not all cryptographic methodologies are completely secure. ZText's architectural framework, based off Zcash's Sapling protocol as well as the zk/SNARKs contains inherent properties that resist quantum decryption in ways that conventional encryption will not. This is due to the fact that what is public and what's covered. Through ensuring your public details aren't disclosed to the Blockchain Z-Text will ensure that there's nothing for a quantum computer to penetrate. All of your conversations in the past, as well as your name, as well as your wallet are kept secure, not due to their own strength, but because of invisible mathematics.
1. A Fundamental Security Risk: Exposed Public Keys
To grasp why Z-Text has the ability to be quantum-resistant to attack, you first need to realize why many systems not. In normal transactions on blockchain, your public key is revealed at the time you purchase funds. A quantum computer may take that exposed public key and through Shor's algorithm generate your private one. Z-Text's encrypted transactions, utilizing z-addresses, never expose to the public key. The zk-SNARK certifies that you own access to the key without revealing. It is forever concealed, giving the quantum computer no way to penetrate.
2. Zero-Knowledge Proofs as Information Maximalism
The zk-SNARKs inherently resist quantum because they depend on the complexity in solving problems that are not easy to solve with quantum algorithms, such as factoring and discrete logarithms. Furthermore, this proof does not provide information regarding the witness (your private password). Although a quantum computer can theoretically alter one of the assumptions behind the proof it's got nothing in its possession. This proof is not a valid cryptographic method that verifies a statement without containing any of its content.
3. Shielded Addresses (z-addresses) as being obfuscated existence
A z-address in Z-Text's Zcash protocol (used by Z-Text) is never published as a blockchain entry in a way that connects it with a transaction. If you get funds or messages, the blockchain only is able to record that the shielded pool transaction took place. The address you have entered is among the merkle-like tree of notes. A quantum computer scanning the blockchain can only see trees and proofs, not leaves and keys. It is encrypted, but it's not observed, rendering it inaccessible to analysis retrospectively.
4. "Harvest Now and Decrypt Later "Harvest Now, Decrypt Later" Defense
One of the greatest threats to quantum technology today does not involve active attacks instead, it's passive collection. Hackers are able to steal encrypted data online and store in a secure location, patiently waiting for quantum computers' development. For Z-Text attackers, they can mine the blockchain, and then collect the transactions that are shielded. However, without viewing keys, and without ever having access to the publicly accessible keys, they're left with none to decrypt. The data they harvest is one of the zero-knowledge proofs designed to will not have encrypted messages which they are able to crack later. The message itself is not encrypted by the proof. The evidence is merely the message.
5. It is important to make sure that you only use one time of Keys
For many cryptographic systems recycling keys results in visible data that can be analysed. Z-Text is based on BitcoinZ blockchain's use of Sapling it encourages the usage of multiple addresses. Every transaction is able to use an illegitimate, unique address stemming from the identical seed. This implies that even there is a chance that one address could be breached (by Non-quantum ways) it is still secured. Quantum resistance is boosted by an ongoing rotation of key keys which limit the impact the value of a cracked key.
6. Post-Quantum Assumptions in zk-SNARKs
Modern zks-SNARKs frequently rely upon equations of curves on elliptic lines, which are theoretically insecure to quantum computers. However, the construction utilized in Zcash and the Z-Text is capable of being migrated. Zcash and Z-Text are designed to eventually support post-quantum secure zk-SNARKs. Because the keys are never revealed, a switch to a fresh proving platform can take place via the protocol itself without being required to share their information about their. The shielded-pool architecture is incompatible with quantum-resistant cryptography.
7. Wallet Seeds and the BIP-39 Standard
Your wallet seed (the 24 words) does not have quantum vulnerability similarly. The seed is actually a large random number. Quantum computers aren't significantly more efficient at brute forcing 256-bit amounts than traditional computers because of the limitations of Grover's algorithm. The problem lies in the generation of public keys using this seed. The public keys are kept from being discovered by using zk_SNARKs, the seed can be protected even during a postquantum age.
8. Quantum-Decrypted Metadata vs. Shielded Metadata
Even if quantum computers eventually cause problems with encryption However, they have the problem that Z-Text hides metadata in the protocol. Quantum computers could reveal that a certain transaction occurred between two parties if they had their public keys. If those keys were not disclosed as well as the transaction is non-zero-knowledge proof and doesn't have any address information, the quantum computer can only see that "something took place in the shielded pool." The social graph, its timing and the frequency are not visible.
9. The Merkle Tree as a Time Capsule
Z-Text records messages on the blockchain's merkle trees of Shielded Notes. The structure itself is resistant quantization because, when you want to search for a particular note one must be aware of its note's committment and position within the tree. Without a viewing key it is impossible for quantum computers to discern your note from millions of notes that are in the tree. The time and effort needed to go through all the trees to locate a particular note is insanely excessive, even with quantum computers. It increases with every block added.
10. Future-Proofing with Cryptographic Agility
Last but not least, the most significant factor in Z-Text's quantum resistant is its agility in cryptography. Since the application is built around a Blockchain protocol (BitcoinZ) which can be modified through consensus of the community, the cryptographic components can be swapped out as quantum threats emerge. Users are not bound to the same algorithm for all time. Additionally, as their history is shielded and their keys are independent of their owners, they're free to shift towards new quantum-resistant designs while not revealing their previous. The technology ensures that conversations remain sealed not just against current threats, but also against the threats of tomorrow.